Enhancing Switch Security: Key Measures for a Reliable Network
Cyber security holds utmost significance in today's interconnected world due to the escalating prevalence of cyber threats and their potential for detrimental financial or reputational consequences. To prioritize comprehensive security measures, businesses should recognize the pivotal role switches play in network security. These critical devices significantly contribute to safeguarding against diverse risks and vulnerabilities. This article emphasizes the significance of mitigating network risks and explores the specific measures implemented by switches to enhance network security.
Common Network Attacks
Enterprises can encounter a multitude of network security threats. Some of the cyber security risks include:
Malware
Malware refers to a type of software with malicious purposes, including viruses, trojans, spyware, etc. Malicious software can be installed in the system without the user's knowledge, and then cause damage to the system or steal data. The purpose of malware includes destroying computer systems, stealing sensitive information, conducting phishing attacks or extortion, etc.
Phishing Attacks
Phishing attacks are a type of network attack that obtains sensitive user information through deception. Attackers often disguise themselves as trustworthy entities, such as banks, email providers, social media platforms, etc. They send false emails and text messages or establish fake websites to lure victims into providing personal information such as usernames, passwords, credit card information, etc. Once the victim provides sensitive information, the attacker can abuse this information for fraud, identity theft, or other malicious activities.
Ransomware
Ransomware aims to decrypt files on infected computers by encrypting them and then extorting victims to pay ransom. Attackers can spread ransomware to the victim's system through email attachments, malicious links, or exploits. Once the ransomware successfully invades the system and encrypts files, the victim cannot access their own data until the requested ransom is paid.
Spyware
Spyware is designed to collect information on a user's computer or mobile device. The user is usually unaware of its existence and activity. Spyware can enter the system by downloading and installing disguised as legitimate software, through malicious links or advertisements, or by manipulating security vulnerabilities. Once spyware is installed on the device, it runs in the background and secretly collects user personal information, browsing habits, sensitive data, and other activities. This information may include login credentials, bank account information, network search records, etc.
DDoS
Distributed Denial of Service (DDoS) attacks are malicious behavior aimed at flooding the target system or network with traffic and requests exceeding normal load, making it unable to provide services to legitimate users normally. In DDoS attacks, attackers typically use botnets to send a large amount of traffic and exploit vulnerabilities to send malicious requests.
SQL Injection Attack
SQL injection attack is a common network security threat that utilizes improper processing of input data by applications to inject malicious SQL code into the application's database. This attack typically occurs in web applications that interact with databases. Attackers attempt to bypass the application's validation and filtering mechanisms by inserting malicious SQL statement fragments into the input fields of the application, directly manipulating the database. Once malicious SQL code is successfully injected, attackers can perform unauthorized database operations such as deleting, modifying, or obtaining sensitive data. This may lead to security issues such as data leakage, system paralysis, illegal access, and information tampering.

Strengthening Switches' Cyber Defences
Here are some suggestions for the cyber security of switches:
Disable Unused Ports
By disabling unused services and protocols, the attack surface of the machine can be reduced. The server administrator usually follows the practice of uninstalling unused roles such as DNS or DHCP. For network switches, unused ports open access to anyone who plugs in an Ethernet cable. Although you may plug cables into all ports, it does not mean that all network interfaces are being used. It is recommended to record all network interfaces in a list at each site in the network. Ports connected to unused interfaces should be disabled. It is good practice to disable all ports when setting up the switch initially, and enable ports one by one when each device needs to go online. Disabling unused ports also helps prevent network loops and potential disruptions caused by users plugging unauthorized devices into open network drops.
Configure Firewall
The firewall serves as a network security system positioned between internal and external networks. Its primary function is to protect internal or private LANs from external attacks and prevent the unauthorized disclosure of sensitive data. In the absence of a firewall, routers simply forward traffic between internal and external networks without any filtering mechanisms. Firewalls play a crucial role by monitoring network traffic and actively blocking unauthorized access attempts. Generally, switches themselves do not have firewall functionality, but some advanced switches can provide firewall functionality. If you have high requirements for network security, it is recommended to configure firewall protection for the switch.
Avoid Using the Default VLAN
It is advisable to avoid relying on default configurations, including default usernames, passwords, and IP addresses. Switches are typically pre-configured with VLAN 1 as the default VLAN, which also serves as the default management VLAN. This information is well-known to experienced hackers. So, how to address this issue effectively? First, it is important to note that users cannot delete VLAN 1, as it is used for switch management communications like CDP and VTP. However, you can choose not to utilize VLAN 1 and create a new VLAN instead. It is recommended to separate data traffic from system chatter by strictly adhering to the rule of not using VLAN 1 for any purpose. Additionally, changing the management VLAN is crucial to deter attackers from easily attempting to establish a management connection.
Filter MAC Address
To control network access, you can enable MAC address filtering on your switch. This associates specific MAC addresses with corresponding physical ports, creating a whitelist of approved MAC addresses. If the switch detects an unapproved MAC address, it denies network access to the device. Additionally, you can blacklist previously unknown or suspicious MAC addresses on the switch to block their access. However, it's important to note that MAC address filtering may not prevent MAC address spoofing attacks, where attackers manipulate their MAC address to deceive the switch or engage in malicious activities.
Choosing High Reliability Switches for Network Security
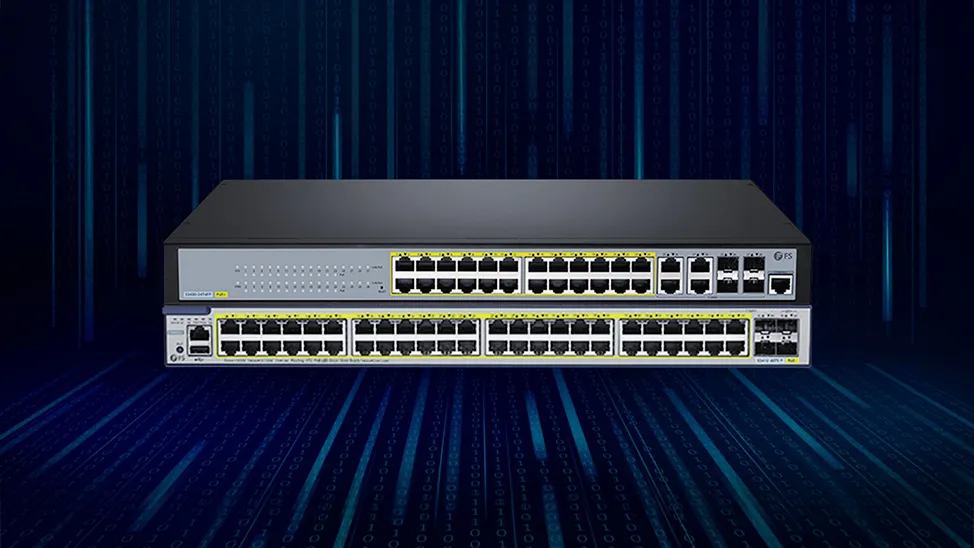
In addition to the above precautions, it is also important to choose a highly reliable switch. In view of this, FS S5860-24XMG and S5860-48XMG switches can be good choices. They offer a comprehensive set of security measures to protect against threats, enforce access control policies, and safeguard sensitive data.
-
Hardware-based IPv6 ACLs: These two switches support hardware-based IPv6 ACLs for configuring rules and filtering conditions on the switch to control and filter IPv6 network traffic. This mechanism can help organizations implement IPv6 traffic management strategies to meet security requirements and reduce network congestion and potential threats.
-
Nessus: FS S5860-24XMG and S5860-48XMG switches are detected by the industry-leading professional scanning tool, Nessus. It can help organizations discover and solve security vulnerabilities in systems, consequently improving network security.
-
DHCP snooping: These switches support Dynamic Host Configuration Protocol(DHCP) snooping, which is a network management protocol used to dynamically assign IP addresses to any device or node on the network, so that it can communicate using IP. DHCP automates and centrally manages these configurations without requiring network administrators to manually assign IP addresses to all network devices. By enabling DHCP snooping, enterprises can effectively protect their networks from the threat of DHCP security vulnerabilities, ensuring that only authorized DHCP servers can provide effective IP address allocation.
-
SSH and SNMPv3: Two switches both support the secure shell (SSH) and SNMPv3, which is a security protocol used to protect network communication and achieve authentication. SSH is used for secure remote login and data transmission on insecure networks. It provides encryption and authentication mechanisms to ensure the confidentiality and integrity of remote access and management communication. Using SSH, all transmitted data is encrypted, which means that even in an insecure network environment, attackers cannot easily eavesdrop, tamper with, or disguise users' login information and data. SNMPv3 is used to monitor and manage network devices, systems, and applications. It provides authentication, encryption, and access control mechanisms to ensure the security and reliability of management communication.
-
NFPP: FS S5860-24XMG and S5860-48XMG switches support network foundation protection policy (NFPP). NFPP usually covers access control, network isolation, defense measures, vulnerability management, logging, and monitoring. By implementing NFPP, enterprises can establish a robust network infrastructure and provide strong security defense and protection mechanisms.

Conclusion
Switches play a significant role in cyber security, especially in today's digital era. Taking actions to protect your data is crucial. When it comes to securing your network against cyber threats, the FS S5860-24XMG and S5860-48XMG switches deliver exceptional performance, making them the ideal choice for organizations seeking a reliable and secure network infrastructure.
Visit FS.com for more information about FS S5860 series switches.
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
May 30, 2024