FS Pica8 Software Helps Automate Your Zero Trust Networking Solution
Zero Trust Networking Solution Overview
In recent years, campus networks have seen significant chang. With the enormous number of gadgets and connections brought home by the IoT and edge waves, the campus has suddenly transformed into a thriving ecosystem of digital users. Although largely positive, it has also increased the likelihood of security breaches.
Zero Trust Networking is a cyber security approach that challenges the traditional security model, assuming that threats can come from both inside and outside the network. It prioritizes identity verification and access controls to enhance security.
PicOS® Zero Trust Network Access Control
Typically, Secured zero trust network access solutions may involve features like port security, MAC address filtering, and other measures to ensure the security of devices connected to the wired network. PicOS® supports the following Secured Wired Access solutions:
-
Verification of Identity: Users and devices are not automatically trusted based on their location or network connection. Instead, identity verification is required for every user and device trying to access resources.
-
Least Privilege Access: Users and devices are granted the minimum level of access necessary to perform their tasks. This principle minimizes the potential damage that can be caused in case of a security breach.
-
Micro-Segmentation: The network is divided into small, isolated segments to contain potential threats. This limits lateral movement within the network and prevents attackers from freely navigating once inside.
-
Continuous Monitoring: Continuous monitoring of user and device behavior helps detect anomalies or suspicious activities. This allows for real-time response to potential security incidents.
-
Multi-Factor Authentication (MFA): Multi-factor authentication is a crucial component of Zero Trust. It adds an extra layer of security by requiring users to provide multiple forms of identification before gaining access.
To establish a more secure and resilient network environment, implementing a Zero Trust Networking solution requires a mix of technology, policy, and user awareness. This strategy is especially important given how dynamic and ever-changing the threat.

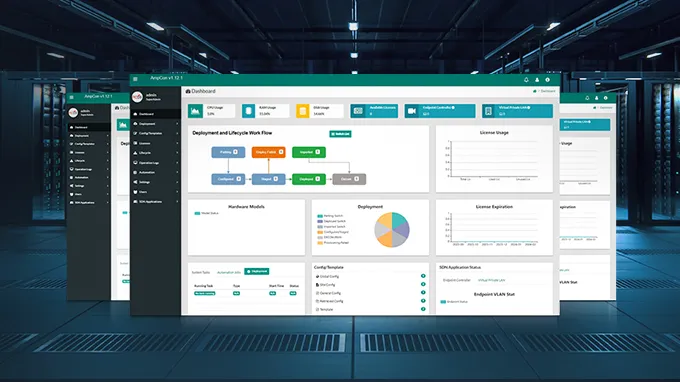
Automate NAC Configuration
Pica8 provides best practice NAC configurations and deployment guides. Its automation tool AmpCon™ provides push-button automation for full lifecycle management. Access switch Network Access Control (NAC) settings can be made more efficient, consistent, and less prone to human error by automating them. The following procedures can be used to zero trust automate NAC configurations:
-
Use Configuration Management Tools: Implement configuration management tools such as Ansible, Puppet, or Chef to automate the deployment and management of network device configurations.
-
Standardize Configuration Templates: Create standardized templates for NAC configurations. Define policies for port security, 802.1X authentication, and other security measures. This ensures consistency across access switches.
-
Continuous Monitoring Automation: Set up automated monitoring for NAC configurations. Implement scripts or tools that regularly check the health and compliance status of devices connected to the network.
-
Testing and Validation Automation: Develop automated tests to validate NAC configurations. Regularly run tests to ensure that the intended security policies are effectively implemented.
-
Dynamic Host Configuration Protocol (DHCP) Integration: Integrate DHCP services with NAC to dynamically assign IP addresses based on device authentication. This helps in automating IP address assignments for compliant devices.
Benefits of PicOS® Zero-Trust Networking
Enhanced Security:
Zero Trust Networking assumes that no entity, whether inside or outside the network, should be trusted by default. This approach significantly enhances overall network security by requiring continuous verification of identities and devices.
Identity Verification:
PicOS®, when aligned with Zero Trust Networking principles, facilitates strong identity verification mechanisms. This includes multi-factor authentication (MFA) and continuous monitoring to ensure that only authorized users and devices gain access.
Adaptive Security Controls:
Zero Trust Networking is dynamic and adaptive, adjusting security controls based on the evolving threat landscape. PicOS® can be configured to adapt its security policies in response to changes in user behavior, device posture, or the overall security environment.
Encryption Support:
PicOS® likely supports encryption protocols to secure communications within the network. This is a critical aspect of Zero Trust Networking, ensuring that data remains confidential and protected from unauthorized access.
Simplified Compliance:
Zero Trust Networking aligns well with various compliance requirements. By implementing strict access controls, continuous monitoring, and other security measures, PicOS® can contribute to maintaining compliance with industry standards and regulations.

Conclusion
In conclusion, FS has established a comprehensive strategic partnership with Pica8. The Pica8 web platform helps create and clearly define zero trust control policies It is crucial to protect network assets from malicious threats. Do you want to konw more about us? FS offers a range of solutions for your business. Book a demo or sign up for a free trial.
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
May 30, 2024