How to Choose the Right Tools for Networking Security Visibility?
In the past, networks were relatively simpler, consisting of a few interconnected devices. Monitoring and managing network traffic was relatively straightforward. However, with the rapid growth of networks and the increasing complexity of modern IT environments, networking visibility has become crucial for organizations to ensure efficient network operations, troubleshoot issues, and enhance network security.
Background of Networking Security Visibility
Networking Security Visibility refers to the ability to monitor, analyze, and gain insights into network traffic and activities. It involves capturing and analyzing data packets flowing through the network to understand the behavior, performance, and security of the network infrastructure. Traditionally, Networking Security Visibility was achieved through network monitoring tools and manual analysis. With increasing network complexity, the need for Networking Security Visibility has grown to ensure efficient network management, troubleshooting, and security. To achieve Networking Security Visibility, organizations deploy various tools and technologies such as Network Packet Brokers (NPBs), network monitoring systems, flow analyzers, intrusion detection systems (IDS), intrusion prevention systems (IPS), and security information and event management (SIEM) solutions.

Why We Need Networking Security Visibility?
Networking security visibility is crucial for organizations to detect and respond to security threats, investigate incidents, comply with regulations, validate security controls, and proactively identify potential risks. It provides the necessary insights and data to protect networks, assets, and sensitive information from unauthorized access, breaches, and other security risks.
-
Threat Detection and Response: Network traffic may be tracked and possible security threats can be quickly identified by businesses thanks to networking security visibility. Organizations can identify dangerous activity including malware infections, illegal access attempts, and data breaches by examining network data and trends. Organizations can limit risks, safeguard vital assets, and respond quickly when they have visibility into network security.
-
Incident Investigation and Forensics: Networking security visibility offers useful information for forensic analysis and investigation in the case of a security incident or breach. Organizations can determine the origin and extent of an incident, comprehend the attack vectors, and obtain evidence for additional investigation or legal needs by looking at network traffic logs and packet captures.
-
Insider Threat Detection: Insider threats pose a significant risk to organizations. Networking security visibility allows organizations to monitor network traffic for unusual or suspicious behavior by authorized users. By analyzing network data, organizations can detect potential insider threats, such as unauthorized access, data exfiltration, or misuse of privileges, and take appropriate actions to prevent or mitigate such risks.
-
Security Policy Validation: Networking security visibility helps organizations validate the effectiveness of their security policies and controls. By monitoring network traffic, organizations can assess whether their security measures, such as firewalls, intrusion detection/prevention systems, or access controls, are functioning as intended. This allows for the identification of potential gaps or vulnerabilities in the security infrastructure and enables organizations to make necessary adjustments to strengthen their security posture.
-
Proactive Threat Hunting: Networking security visibility enables proactive threat hunting, where organizations actively search for potential threats or vulnerabilities within their network. By analyzing network traffic, organizations can look for indicators of compromise, suspicious patterns, or emerging threats that may not be detected by traditional security controls. This proactive approach helps organizations stay ahead of potential threats and strengthens their overall security defenses.
-
Compliance and Auditing: Many industries and organizations have regulatory compliance requirements that mandate the monitoring and auditing of network activities. Networking security visibility tools help organizations meet these requirements by providing the necessary insights and data for compliance reporting. Visibility into network security incidents and controls ensures adherence to industry regulations and standards.
-

Factors That Need to Be Considered
-
Security Requirements: Assess your organization's specific security requirements and objectives. Consider the types of threats you need to defend against, the sensitivity of your data, and any industry-specific compliance regulations you must adhere to. This will help determine the necessary features and capabilities of networking security visibility tools.
-
Network Environment: Evaluate the size, complexity, and architecture of your network environment. Consider the number of devices, network segments, and traffic volume. Determine if you have a distributed network, virtualized environments, cloud-based infrastructure, or remote offices, as these factors may impact the choice of visibility tools.
-
Monitoring Capabilities: Determine the level of visibility you require. Look for tools that provide comprehensive monitoring capabilities, such as the ability to capture and analyze network traffic at different layers of the OSI model. Consider whether you need deep packet inspection, flow analysis, or application-level visibility.
-
Scalability and Performance: Consider the scalability and performance requirements of your organization. Will the networking security visibility tools be able to handle the volume of network traffic and provide real-time analysis without a significant impact on network performance? Ensure that the tools can scale as your network grows.
-
Integration with Existing Infrastructure: Assess the compatibility and integration capabilities of the networking security visibility tools with your existing network infrastructure and security systems. Determine if the tools can integrate with firewalls, intrusion detection/prevention systems, SIEM solutions, or other security controls to provide a holistic view of your network security.
By considering these factors, organizations can choose networking security visibility tools that align with their specific security requirements, network environment, and operational needs. It's important to evaluate multiple options, conduct proof-of-concept trials if possible, and involve key stakeholders to make an informed decision.
What Kind of Tools That Networking Security Visibility Need?
Several tools are commonly used for networking security visibility:
-
Network TAPs (Traffic Access Points): TAPs provide passive access to network traffic, enabling full visibility without interfering with network performance. They capture and copy network packets for analysis by security tools.
-
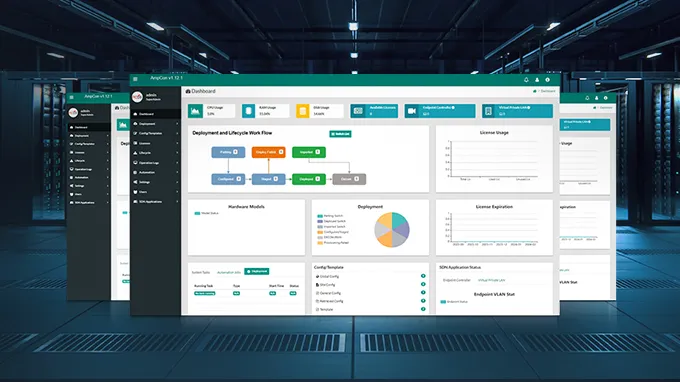
Network Packet Brokers (NPBs): NPBs aggregate, filter, and distribute network traffic to various security and monitoring tools. They optimize traffic distribution, load balancing, and provide advanced features like deduplication and SSL decryption.
-
Network Monitoring Tools: Tools like Wireshark, tcpdump, and SNMP-based network monitoring systems capture and analyze network traffic, providing visibility into network performance and identifying security issues.
-
Security Information and Event Management (SIEM) Systems: SIEM solutions collect, correlate, and analyze log data from various security devices and systems, providing centralized visibility into security events and enabling effective incident response.
-
Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS): IDS/IPS solutions monitor network traffic for suspicious activities and potential security breaches. They provide real-time alerts and can take proactive measures to prevent attacks.
-
Security Analytics Platforms: These platforms integrate and analyze data from multiple security sources, including network traffic, logs, and threat intelligence, to provide advanced threat detection, incident response, and security analytics.
These tools work together to provide comprehensive visibility into network traffic, performance, and security. Depending on the specific requirements and goals of an organization, a combination of these tools may be used to achieve effective networking security visibility.
How to Choose Networking Security Visibility Tools:
When choosing networking security visibility tools, consider the following:
-
Identify Requirements: Determine the specific visibility requirements based on security goals, compliance needs, network size, and operational challenges.
-
Research and Evaluate: Research different tools available in the market, assess their features, scalability, compatibility, and user reviews. Evaluate how well they align with your requirements.
-
Proof of Concept (PoC): Perform a PoC with shortlisted tools to assess their performance, ease of use, and compatibility with your network infrastructure. Verify if they meet your specific needs.
-
Cost and ROI: Consider the total cost of ownership, including licensing fees, maintenance, and infrastructure requirements. Evaluate the return on investment (ROI) based on the value provided by the tools.
-
Vendor Support and Reputation: Assess the vendor's reputation, customer support, and their track record in delivering reliable and effective solutions.
-
Integration and Interoperability: Ensure that the selected tools can integrate with your existing security infrastructure, management systems, and other tools to provide comprehensive visibility.
-
Scalability and Future Needs: Consider the scalability of the tools and their ability to accommodate future growth and changing network requirements.
By carefully evaluating these factors, organizations can choose the most suitable networking security visibility tools that align with their specific requirements and provide effective network monitoring, threat detection, and incident response capabilities.
Conclusion:
Overall, networking security visibility is an essential aspect of modern network management and security. It empowers organizations to proactively protect their networks, assets, and sensitive information, detect and respond to security incidents, and ensure compliance with industry regulations. By investing in the right networking security visibility tools, organizations can strengthen their overall security posture and mitigate risks in today's evolving threat landscape.
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
May 30, 2024