Understanding Virtual LAN (VLAN) Technology
What Is VLAN and Why It Is Used?
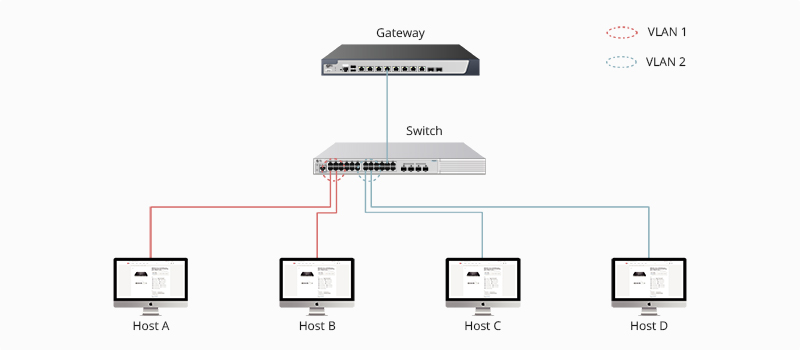
As the scale and complexity of enterprise networks continue to expand, traditional Local Area Network (LAN) architectures face increasingly significant challenges. Just like the following LAN application topology showed, in order to communicate with host B, host A will broadcast its ARP (address resolution protocol) request to all the VLAN switches and other hosts over the same local area network.

When the network is bombarded with hosts and switches, it’s likely to lead to broadcast storms. The broadcast storms and declining network efficiency caused by a single broadcast domain have become bottlenecks hindering smooth communication and effective resource utilization. Consequently, the hosts’ CPU and the bandwidth of the whole network will be greatly consumed. To solve that, VLAN technology arrives.

By configuring VLANs, you can divide a network into different broadcast domains. Packets sent from workstations on one network segment are transmitted by Bridges or VLAN switches that do not forward conflicts but broadcast to each network device. This simplifies many of the potential complications caused by Lans, including excessive network traffic and conflicts. In this way, network resources and bandwidth will be greatly saved, improving network flexibility and performance.
Types of VLANs
VLAN technology play a pivotal role in the networking systems of organizations with complex infrastructures. These solutions enable network scaling, segmentation for enhanced security, and reduction of network latency. While Local Area Networks (LANs) connect devices to a server using cables, VLANs facilitate communication among multiple LANs and associated devices through wireless internet. The following outlines five distinct types of virtual networks.
Management VLAN
A strategically designed compact network for overseeing incoming traffic from devices, application logs, and monitoring processes. Its key advantage lies in enhanced network security by minimizing broadcast radiation impact. Access restrictions and redirection of regular traffic to other virtual networks contribute to a safer network.
Voice VLAN
Configured to carry voice traffic, this network preserves bandwidth and enhances Voice over IP (VoIP) quality. It prioritizes traffic from VoIP equipment and devices like IP phones, VoIP endpoints, and voice systems, ensuring high transmission priority over other network traffic.
Native VLAN
Used in traditional systems or devices lacking VLAN support, this network serves as a common identifier on trunk links. It carries untagged traffic from systems or devices configured with the native VLAN via switch ports.
Default VLAN
Serving as a default network for all access ports until assigned to other networks, such as voice or management VLANs. The default virtual network facilitates interconnection among diverse devices. Furthermore, it retains an immutable status, impervious to renaming or deletion.
Data VLAN
Dividing the network into two main groups—users and devices—this network exclusively carries user-generated data. Unlike management or voice VLANs, it does not handle management or voice traffic, enabling administrators to group users even if not connected to the same network switch.
How Does VLAN Work?
Intra-VLAN Communication
Intra-VLAN communication refers to the communication of users in the same network segment and VLAN. Generally, this type of VLAN is applied into two scenarios: intra-VLAN communication through the same device and intra-VLAN communication through multiple devices. No matter what type, the whole transmission process mainly goes through the following two steps:
-
ARP Request from the Source Host: Before sending, the source host will compare its IP address with the designation’s. If the source host finds that they are in the same network segment, it will get destination host’s MAC address and fill the destination field MAC address of the frame with the obtained MAC address. On the contrary, the broadcast packet needs to be sent to the gateway. The MAC address of gateway will be used by the source host as its destination MAC address.
-
VLAN Tag Manipulation during Device Communication: When frames processed in a VLAN switch, VLAN tags need to be carried.
Inter-VLAN Communication
Since broadcast packets are limited in the same VLAN, hosts in different VLANs are unable to directly communicate with each other in layer 2. Therefore, inter-VLAN routing that can forward network traffic from one VLAN to another is used to solve this problem. There are three options available in order to enable routing between different VLANs:
-
Inter-VLAN Routing with Separate Physical Interfaces:This inter-VLAN routing way is to connect an additional port from each VLAN with a router. Each VLAN needs one physical port on the router, which causes the great cost of routers. Therefore, this type of inter-VLAN routing has been rarely used due to its high cost and poor scalability.
-
Router-on-a-Stick Inter-VLAN Routing:This type of VLAN routing enables one single physical interface to achieve traffic forwarding between VLANs. After configuring the connection between the router and the VLAN switch as a trunk link, the router can receive frames with VLAN tags on the trunk interface from the connected switch, and forward the routed packets out to VLAN tagged destinations via the same interface.
-
Inter-VLAN Routing with Layer 3 Switch:The last method is to use layer 3 switches with routing function. Users need to create a SVI (Switch Virtual Interface) for each VLAN and configure an IP address for it. This IP address can be used for computers as their default gateway. In that way, the packets from one VLAN will be sent to the SVI to be routed to the other VLANs to realize the inter-VLAN communication.

Advantages of VLAN
Reduced Broadcast Domains
By confining the broadcast domains, end-stations on a VLAN are prevented from listening to or receiving broadcasts not intended for them. Moreover, if a router is not connected between the VLANs, the end-stations of a VLAN cannot communicate with the end-stations of the other VLANs. Confinement of broadcast domains on a network significantly reduces traffic.
-
Example: In a large company, different departments use separate VLANs. This ensures that broadcast traffic from one department doesn't affect others, improving network efficiency.
Enhanced Network Security
Virtual boundaries created by a VLAN can only be crossed by routers. Therefore, access to the VLAN can be restricted using standard router-based security measures. In addition, VLANS can enhance network security through packet filtering. Network administrators control each port and any resources they allow to be used, separating groups with sensitive data from the rest of the network and reducing the chance of confidential information leaking.
-
Example: In a healthcare network, patient data and medical devices are in different VLANs. Tight control via VLANs ensures only authorized personnel can access medical device VLAN, ensuring patient privacy.
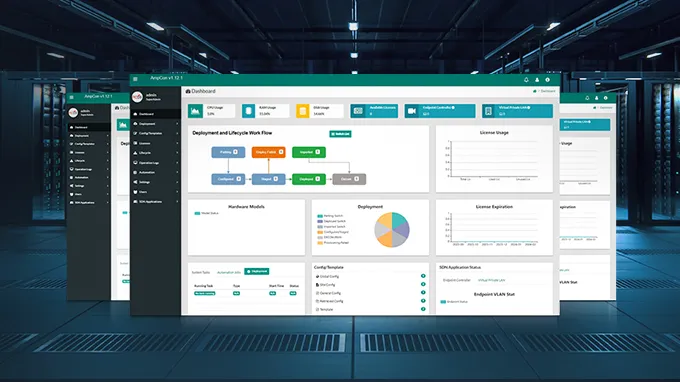
Simplified Network Management
VLAN technology significantly enhances the ease of network management by grouping users with similar network requirements into the same VLAN. When introducing a new VLAN switch, the process of adding or modifying network nodes becomes swift and straightforward through the web management page. All policies and procedures configured for a specific VLAN are seamlessly executed upon port allocation. The IT staff finds it convenient to discern the functionality of a VLAN through appropriately labeled names.
-
Example: A multinational corporation uses VLANs to manage employees in different regions. VLANs enable quick adjustments through a central system, simplifying network management.
Effortless Device Management
VLANs streamline project and application management, consolidating users and network devices to align with business or geographical needs. The segregation of capabilities facilitates the efficient administration of projects or dedicated applications. Devices can be logically grouped based on functionality, providing a more intuitive management approach than traditional location-based methods.
-
Example: In a university network, VLANs logically group teaching, student, and admin devices. This makes it easy for IT to manage different devices, like configuring all teaching devices in a VLAN centrally.
Conclusion
VLAN technology provides a sophisticated solution for network segmentation, enhancing security, reducing broadcast storms, and simplifying management. Their benefits include minimized broadcast domains and improved network security, making VLAN technology essential for efficient and secure operations.
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
May 30, 2024