IDS vs IPS vs Firewall: Which Do You Need?
To keep their network secure and guard against threats, most corporate networks employ a variety of networking tools and techniques. Among the most crucial defenses are firewalls and IDS/IPS systems. In this article, we will explore these three defenses in detail, highlighting their functions and differences.
What is a Firewall?
A firewall is a network security device that monitors and filters incoming and outgoing network traffic based on predefined security rules. Installed at the network's perimeter, firewalls serve as the first line of defense, ensuring that all data packets pass through them before entering or leaving the network. Their primary function is to prevent unauthorized access by evaluating data packets based on criteria such as IP addresses and port numbers. Firewalls analyze these packets and decide whether to allow, deny, or reject them according to the established rules. This process helps to protect the network from external threats and unauthorized access.
For instance, the FS NSG-5220 next-generation firewall designed to offer robust security features and high performance. Equipped with a rich selection of ports and boasting impressive speeds such as 20 Gbps Firewall Throughput and 5.5 Gbps NGFW Throughput. This firewall series not only ensures high security performance but also supports comprehensive advanced threat detection and prevention.

What is an IDS?
An intrusion detection system (IDS) is a cybersecurity tool or software designed to monitor network or system activities for malicious actions or policy violations. It identifies potential security threats by analyzing network traffic and system behavior, looking for anomalies or patterns indicative of unauthorized access or attacks. When a potential threat is detected, the IDS alerts administrators, allowing them to take appropriate measures to protect the network.
What is an IPS?
An intrusion prevention system (IPS) is a security tool that actively monitors and analyzes network traffic to identify and block potential threats. Positioned inline with network traffic, typically just beyond the firewall, an IPS can take immediate action by blocking harmful data packets, alerting administrators, or severing connections. It uses various detection methods such as signature-based, anomaly-based, and policy-based detection to protect the network. Unlike an IDS, which only detects and reports threats, an IPS prevents them, offering a more advanced level of security.
Firewall vs. IDS vs. IPS:Differences
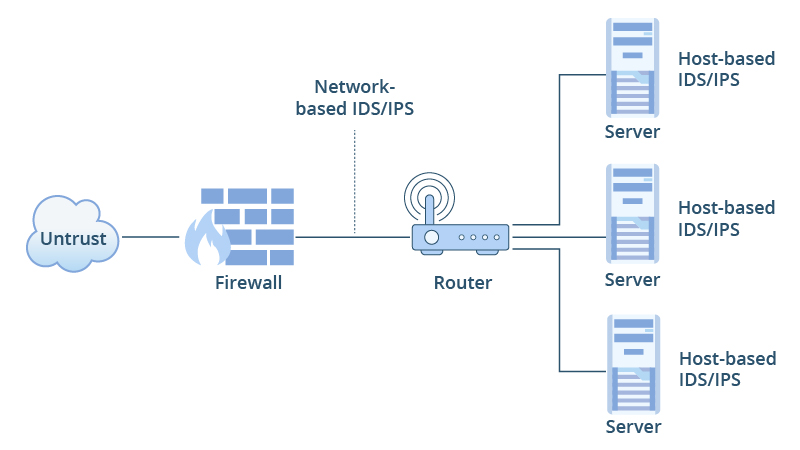
The primary distinction between firewalls, IDS, and IPS lies in their roles and actions regarding network security. An IDS/IPS detects and notifies a system administrator of an attack or, depending on its configuration, stops it, while firewalls perform actions such as blocking and filtering traffic.
Working Principle: A firewall filters traffic based on IP addresses and port numbers, acting as a barrier between trusted and untrusted networks using predefined security rules. An Intrusion Detection System (IDS) monitors real-time traffic for attack patterns, generating alerts when suspicious activity is detected. An Intrusion Prevention System (IPS) not only detects these threats but also actively blocks them by analyzing real-time traffic for known patterns or anomalies.
Function: The primary function of a firewall is to monitor and manage traffic according to pre-established security rules, preventing unauthorized access. An IDS identifies and alerts administrators of potential threats without taking direct action. In contrast, an IPS actively blocks malicious traffic, providing proactive defense.
Location: A firewall is typically placed at the network perimeter, serving as the first line of defense against external threats. An IDS is usually located within the internal network to monitor traffic without interfering with data flow. An IPS can be deployed anywhere in the network but is often positioned just beyond the firewall to block threats in real-time.
Traffic Filtering: A firewall filters traffic based on pre-established rules without analyzing traffic patterns. An IDS examines traffic behavior to detect malicious patterns and generates alerts. An IPS also examines traffic behavior but takes additional steps to block malicious traffic.
Performance Impact: A firewall generally has minimal impact on network performance since it uses simple rules to filter traffic. An IDS can significantly impact performance depending on the complexity of its traffic analysis and the volume of alerts. An IPS may substantially affect performance due to real-time traffic analysis and active threat mitigation.
Which Approach Do You Need?
When and how to select intrusion protection solutions among the three defense options? Two viewpoints are examined in the analysis that follows:
-
Product value: The monitoring of cyber security status is the main objective of intrusion detection systems. The management of incursion behavior is the main goal of an intrusion prevention system. Intrusion prevention systems can implement deep defense security strategies, which allows them to detect and prevent attacks at the application layer. This is something that firewalls and intrusion detection products are unable to do. In contrast, intrusion prevention systems can implement security strategies.
-
Product application: The intrusion detection system must be installed at the network center and have the ability to monitor all network traffic to fulfill the goal of fully detecting cyber security status. To control the security status of the entire information system, distributed deployment—deploying an intrusion detection analysis engine for each subnet and unifying the engine's policy management and event analysis must be implemented if the information system is made up of several logically isolated subnets.
Considering the above two points, enterprises can choose different intrusion prevention products according to their defense needs to bring better security protection to enterprise cyber security.
Conclusion:
It is essential to comprehend the distinctions between firewalls and IDS/IPS to put a robust cyber security plan into action. Firewalls serve as barriers to stop unauthorized users from accessing networks, whereas IDS/IPS monitors network activity to give a deeper examination and identification of possible security concerns. To improve company cyber security, this article should be able to assist you in selecting various intrusion prevention solutions based on your specific needs.
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
May 30, 2024