Network Switch vs Network Router vs Network Firewall
There are three basic devices that are utilized in almost every network—network switch, network router and network firewall. They can be integrated into one device for small size networks such as for home networking, but it will not be the case for larger networks. For any network, none of the three devices can be dismissed. Learn to know how they work and how they build your network in this post.
Switch—Bridge Your Devices in a Network
In a local area network (LAN), network switch functions similar to the overpasses in cities that bridge other network devices, like switches, routers, firewalls and wireless access points (WAPs), and connect client devices, such as computers, servers, Internet Protocol (IP) cameras and IP printers. It provides a central place of connections for all the different devices on the network.

Figure 1: Switches bridge different network devices and client devices like overpasses in cities.
How Does a Switch Work?
A switch switches data frames by keeping a table of what Media Access Control (MAC) addresses have been seen on which switch port. MAC address is a burnt-in mark in the hardware of a network interface controller (NIC). Every network card and every port of switches and routers has a unique MAC address. The switch learns the source and destination MAC addresses from the data frames and keeps them in the table. It refers to the table to determine where to send the frames that it receives. If it receives a destination MAC address that it does not have in the table, it floods the frame to all switch ports, which is known as broadcast. When it receives a response, it puts the MAC address in the table and it needs not to flood next time.
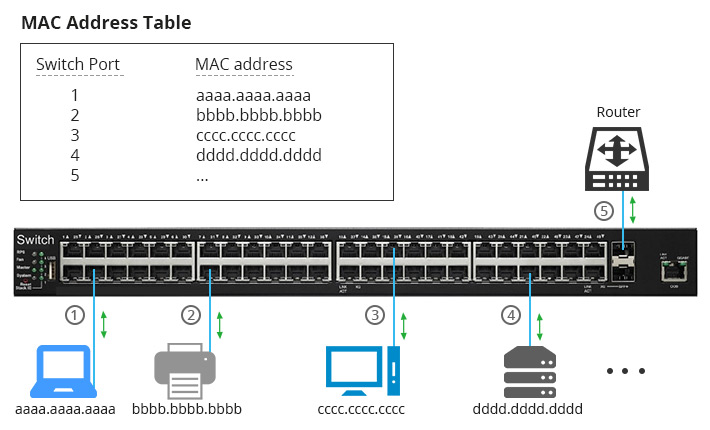
Figure 2: A switch learns MAC addresses from the data frames.
Router—Connect You with the Internet
Routers (sometimes called Gateways) are hardware devices used to route packets between different networks, and to connect your network with the Internet. In fact, the Internet is made up by hundreds of thousands of routers.
How Does a Router Work?
A router checks the source and destination IP addresses of each packet, looks up the destination of the packet in the router’s IP routing table, and routes the packet to another router or a switch. The process keeps happening until the destination IP address is reached and responds back. When there is more than one way to go to the destination IP address, routers can smartly choose the most economical one. When the destination of the packet is not listed in the routing table, the packet will be sent to the default router (if it has one). If there’s no destination existing for the packet, it will be dropped.
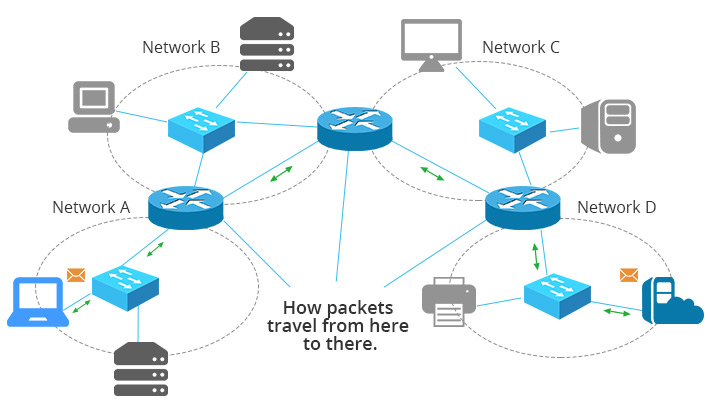
Figure 3: How routers route packets from the source to the destination.
Generally, your router is provided by your Internet Service Providers (ISP). Your Internet provider assigns you one router IP address, which is a public IP address. When you browse the Internet, you’re identified to the outside world by the public IP address and your private IP address is protected. However, the private IP addresses of your desktop, laptop, iPad, TV media box, network copier are completely different. Otherwise, the router cannot recognize which device is requesting what.
What Does a Router Do?
Routers interpret different networks. Apart from the most commonly used Ethernet, there are many other different networks, such as ATM and Token Ring. The networks encapsulate data in different methods so they cannot communicate directly. Routers can “translate” these packets from different networks so they can understand each other.
Routers prevent broadcast storm. Without a router, a broadcast will go to every port of every device and be processed by every device. When the amount of broadcasts is too large, chaos can occur in the whole network. A router subdivides the network into two or more smaller networks that are connected by it, and it won’t allow the broadcast to flow between subnets.
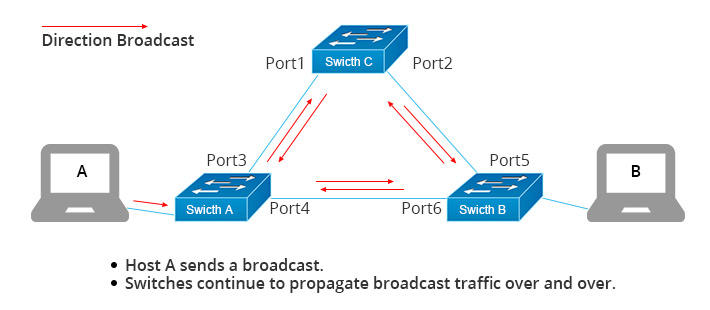
Figure 4: Broadcast storm occurs when there is a large amount of broadcasts.
Switches vs. Routers
Why to compare switches vs. routers? Because Layer 3 switches are able to do routing. Someone may ask why not just use an L3 switch then you need no router at all. Every device has its own features and the choice depends on many factors. On one hand, for instance, for a small network with 10-100 users, an L3 switch is an overkill with regard to the cost or the functionality. An appropriate router can do the job well at a fair cost. On the other hand, you can have switching modules on routers to make it work like a L3 switch according to your needs. So the point of which device to use should consider its scalability, resiliency, software features, hardware performance, etc.
Firewall—The One Who Safeguard Your Network
Firewalls are literally walls used to block fires in emergency. Network firewall sets up a barrier between an intranet/LAN and the Internet. Generally, a network firewall protects an internal/private LAN from outside attack and prevents important data to leak out. While routers without firewall capability blindly pass traffic between two separate networks, firewalls monitor the traffic and block unauthorized traffic out.
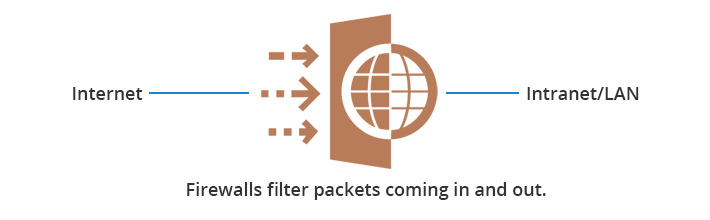
Figure 5: Firewalls set up a barrier between the Internet and the intranet/LAN.
In addition to separating the LAN from the Internet, network firewalls can also be used for segmenting important data from ordinary data within a LAN. So that internal invasion can also be avoided.
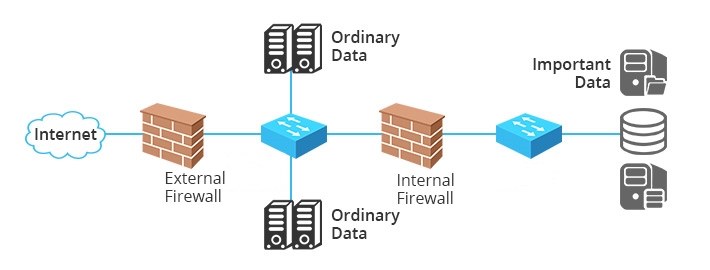
Figure 6: Internal firewall separates important data from others.
How Does a Network Firewall Work?
One common type of hardware firewall allows you define the blocking rules, such as by IP address, by Transmission Control Protocol (TCP) or User Diagram Protocol (UDP) of the port. So unwanted ports and IP addresses are forbidden. Some other firewalls are software applications and services. Such firewalls are like a proxy server which interconnect the two networks. The internal network does not communicate with outside network directly. The combination of these two types is usually safer and more efficient.
Switch, Router & Firewall: How Are They Connected?
Usually router is the first thing you will have in your LAN, a network firewall is between the internal network and the router so that all flows in and out can be filtered. Then the switch follows. Since many Internet providers are now providing Fiber Optic Service (FiOS), you need a modem before the network firewall to turn the digital signal to electrical signals that could be transmitted over Ethernet cables. So the typical configuration would be Internet-modem-firewall-switch. Then the switch connects other network devices.
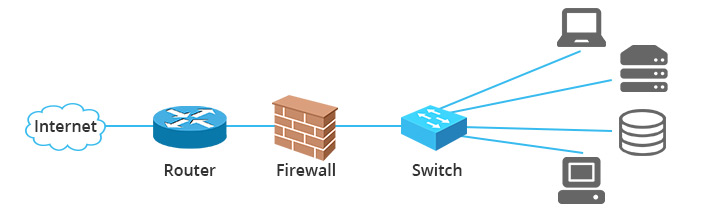
Figure 7: How switch, router and firewall are connected in a network.
Summary
Switches enable internal communication in your LAN; routers connect you to the Internet; firewalls secure your network. All the three components are indispensable in a network. Small networks may have an integrated device of the three, while large networks like enterprise networks, data centers, your Internet service providers will have all these three to keep multiple, complex and highly-secured communications.
Related Article: Managed vs Unmanaged Switch: Which One Can Satisfy Your Real Need?
Related Article: Comparison Between Store-and-Forward Switching and Cut-Through Switching
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
Mar 16, 2023














