What Is IGMP Snooping?
Traditional network unicast mode fails to meet today’s data transmission requirements as it instead increases network load and consumes network bandwidth greatly. To solve the problem, IGMP (Internet Group Management Protocol) Snooping is developed and now widely configured on network multicast mode. What is IGMP Snooping? How does multicast IGMP Snooping work? And what should you know about IGMP Snooping configurations? All of these questions will be explained in this post.
What Is IGMP Snooping?
IGMP, an important feature of network multicast, is used to establish and manage memberships of hosts and routing devices in a multicast group. And IGMP Snooping controls these multicast groups by snooping and analyzing the multicast packets exchanged between the upstream Layer 3 multicast device and downstream hosts, so as to effectively suppress the unnecessary forwarding of multicast data in Layer 2 networks.
How Does IGMP Snooping Work?
In a LAN, multicast packets must pass through Layer 2 switches between the router and multicast users. However, multicast packets may be broadcast to all the hosts in the broadcast domain including non multicast group members, as the Layer 2 switch cannot learn multicast MAC addresses. This wastes network bandwidth and threatens network information security.
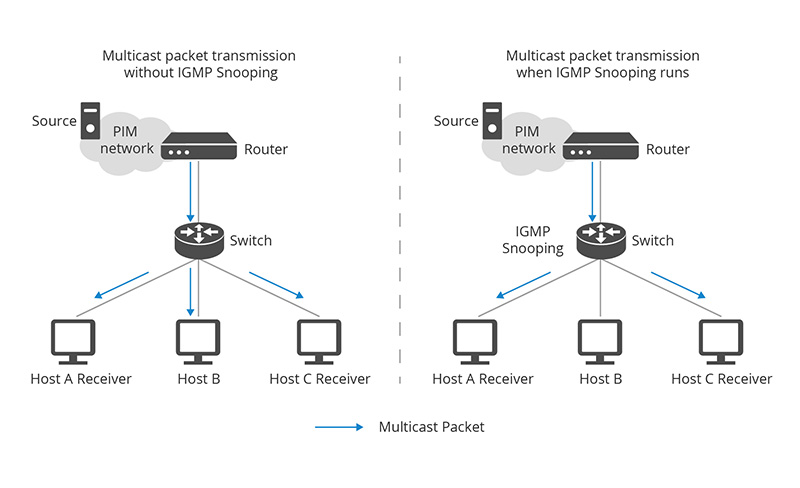
IGMP Snooping solves this problem. As shown in the above figure, when IGMP snooping is not running on the switch, multicast packets are broadcast to Host A, B, C. But when IGMP snooping is enabled, the IGMP Snooping switch can listen to and analyze IGMP message and set up Layer 2 multicast forwarding entries to control multicast data forwarding. In this way, multicast packets are only multicast to multicast group members host A and C receivers, rather than broadcast to all hosts.
What Are Functions and Applications of IGMP Snooping?
As previously mentioned, two main benefits of IGMP Snooping switch are preventing bandwidth waste and network information leakage.
Multicast Snooping helps network switches supporting IGMP Snooping and routers to efficiently transmit multicast data packets to the designated receivers. Its important values become more clear when a filtering method of multipoint transmission is missing: the incoming multicast packets are broadcast to all hosts in the broadcast domain. Especially in larger networks, IGMP Snooping switch reduces unnecessarily high traffic which can even lead to network congestion. Criminals can take advantage of this safe leak and flood individual hosts or the entire network with multicast packets to break them down, just like a typical DoS/DDoS attack.
If IGMP snooping command is enabled, bandwidth wastes and hostile attacks like these will be optimized greatly. All downstream hosts only receive multicast packets for which they have previously registered via group requests. Using network switch supporting IGMP Snooping is therefore worthwhile wherever a great deal of bandwidth is required. Examples include IPTV and other streaming services as well as web conference solutions. However, networks with only a few subscribers and hardly any multicast traffic does not benefit from the filter procedure. Even if the switch or router offers the multicast IGMP Snooping feature, it should remain off to prevent unnecessary eavesdropping.
Considerations on IGMP Snooping Configurations
Basic IGMP snooping functions enable a device to create and maintain a Layer 2 multicast forwarding table and implement on- demand multicast data transmission at the data link layer. Before configuring IGMP snooping functions, you should consider the following elements.
IGMP Snooping Querier
For the purpose of enabling IGMP Snooping, a multicast router must be deployed in the network topology to generate IGMP queries. Without a querier, IGMP membership reports and group membership tables cannot be retrieved and updated regularly, resulting in the unstable working of IGMP Snooping. When IGMP Snooping querier is configured, it sends out IGMP queries on a timed interval to generate IGMP report messages from the network switch with multicast memberships. And IGMP Snooping listens to these IGMP reports to establish appropriate forwarding.
IGMP Snooping Proxy
IGMP Snooping proxy is an enhanced function. When enabled, the IGMP Snooping switch starts working as IGMP Snooping does, and then, when the switch retrieves an IGMP query from a router, it promptly responds with a report according to its status. When disabled, the IGMP queries in VLAN and the reports from hosts are flooded. Thus IGMP Snooping proxy prevents a sudden burst in IGMP report traffic in response to queries and reduces the reports IGMP querier needs to process. However, latency is introduced when propagating the IGMP state through the VLAN.
IGMP Snooping Version
IGMP has three protocol versions: V1, V2, and V3. Correspondingly, you can choose an IGMP snooping version on a Layer 2 device to process IGMP messages in different versions. Generally, IGMPv1 identifies the queried router based on the multicast routing protocol. IGMPv2 adds the capability of group-queries, allowing the querier to send messages to the hosts in a multicast group. IGMPv3 brings more improvements to support specific source filtering.
Conclusion
IGMP snooping is an important feature of network switches. When it is enabled, the bandwidth consumption will be reduced in a multi-access LAN environment so as to avoid flooding the entire VLAN, and network information security can also be improved at the same time. Thus figuring out IGMP Snooping configurations and functions helps you build an optimized network.
Related Article
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
Mar 16, 2023














