Basic Switch Security Concepts Explained
Switches play a vital role in network infrastructure by facilitating the flow of data packets between devices. While switches provide efficient connectivity, it is crucial to implement appropriate security measures to protect networks from unauthorized access and potential attacks. In this article, we will explore basic switch security concepts and best practices to ensure a secure network environment.
How Does a Switch Provide Security?
A switch offers several security features that can be employed to safeguard network communications and prevent unauthorized access. Let's delve into two fundamental switch security concepts: secure remote access and switch port security.
Secure Remote Access
Remote access to switches allows network administrators to manage and configure devices from a remote location. However, it is imperative to secure this access to prevent unauthorized individuals from compromising the network. One commonly used method for secure remote access is Secure Shell (SSH).
SSH operates by encrypting data transmitted between the administrator's device and the switch, ensuring that sensitive information remains confidential. By implementing SSH, organizations can establish a secure channel for remote management, minimizing the risk of data interception or unauthorized access.

Switch Port Security
Switch port security involves implementing measures to secure individual switch ports, preventing unauthorized devices from gaining network access. There are various techniques to enhance switch port security, including:
Secure Unused Ports: Disable unused switch ports to prevent unauthorized devices from connecting to the network. By deactivating these ports, organizations reduce the potential attack surface and minimize the risk of unauthorized access.
DHCP Snooping: Dynamic Host Configuration Protocol (DHCP) snooping is a security mechanism that mitigates DHCP-related attacks. It ensures that only authorized DHCP servers can assign IP addresses to devices connected to the switch. DHCP snooping prevents rogue DHCP servers from distributing incorrect or malicious IP configurations, enhancing network security.
Port Security: Port security allows administrators to define the number of MAC addresses that can be learned on a specific port. In the event of a violation, where an unauthorized device attempts to connect, administrators can configure violation modes. These modes can include shutting down the port, sending an alert, or dynamically assigning the unauthorized MAC address to a specific VLAN for isolation.
Switch Security Concerns in LANs
Local Area Networks (LANs) often face specific security concerns that must be addressed to ensure the integrity of network communications. Let's explore two common security attacks in LANs: MAC address flooding and DHCP spoofing.
Common Security Attacks: MAC Address Flooding
MAC address flooding occurs when an attacker floods the switch with numerous fake MAC addresses, overwhelming the switch's MAC address table. This can lead to a scenario where the switch enters a fail-open mode, allowing all traffic to pass through without proper MAC address validation. Implementing port security measures, such as limiting the number of MAC addresses per port, can mitigate MAC address flooding attacks.

Common Security Attacks: DHCP Spoofing
DHCP spoofing involves an attacker pretending to be an authorized DHCP server, distributing incorrect or malicious IP configurations to devices. This can result in network disruptions, unauthorized access, or eavesdropping on network traffic. DHCP snooping, as mentioned earlier, provides an effective defense against DHCP spoofing attacks by validating DHCP server legitimacy and ensuring only authorized servers are utilized.
Switch Security Best Practices
To enhance switch security, organizations should adhere to the following best practices:
Regularly Update Firmware: Keep switch firmware up to date with the latest security patches and bug fixes. Regular updates ensure that potential vulnerabilities are addressed, reducing the risk of exploitation.
Enable Port Security: Implement port security features to restrict unauthorized access. This includes disabling unused ports, limiting the number of MAC addresses per port, and configuring violation modes to respond to security breaches.
Implement Access Control: Enforce strong access control measures, including secure authentication methods such as using strong passwords, implementing two-factor authentication, and limiting administrative access to trusted individuals. This helps prevent unauthorized individuals from gaining access to the switch and compromising the network.
Implement VLANs: Virtual Local Area Networks (VLANs) provide segmentation within the network, isolating different groups of devices from one another. By separating devices into VLANs based on their functions or security requirements, organizations can mitigate the impact of potential security breaches and limit lateral movement within the network.
Monitor Network Traffic: Implement network monitoring tools to detect and analyze network traffic for any suspicious or malicious activities. Intrusion Detection Systems (IDS) and Intrusion Prevention Systems (IPS) can help identify and respond to potential threats in real time, providing an additional layer of security.
Regular Audits and Penetration Testing: Conduct regular audits of switch configurations and network security policies to ensure compliance with best practices. Additionally, performing periodic penetration testing helps identify vulnerabilities and weaknesses in the network infrastructure, allowing organizations to address them proactively.
Educate Users: Human error is a significant factor in network security breaches. Educate users about basic security practices, such as avoiding clicking on suspicious links or opening attachments from unknown sources. By promoting a culture of security awareness, organizations can significantly reduce the risk of successful attacks.
Conclusion
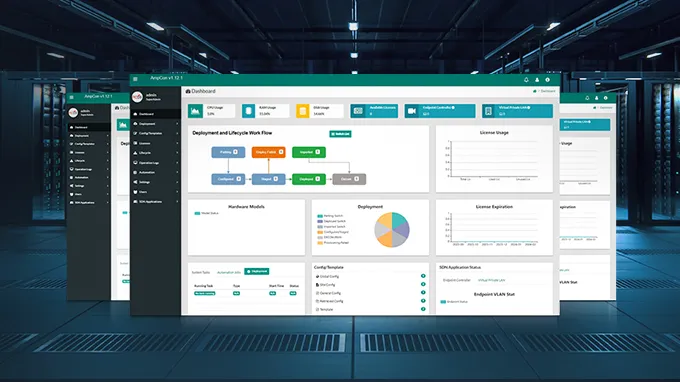
Switch security is a crucial aspect of maintaining a secure network infrastructure. By understanding and implementing basic switch security concepts, organizations can protect against unauthorized access, mitigate potential attacks, and ensure the integrity of network communications. If you're looking to enhance the security of your network environment, FS support team is your ultimate resource.
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
May 30, 2024