What's the Difference Between SSH and SSL?
In today’s digital age, security is a top priority. Two common protocols that help secure data are SSH and SSL. Knowing the key differences between these protocols can help you choose the right one for your needs. Let's dive into what sets them apart.
What is SSH?
SSH, or Secure Shell, is a cryptographic network protocol used for secure communication over an unsecured network. It primarily provides secure access to a remote computer. When you use SSH, you can execute commands, manage files, and run software on another machine as if you were physically present.

What is SSL?
SSL, or Secure Sockets Layer, is a standard security protocol for creating encrypted links between a web server and a browser. SSL ensures that data transferred between the web server and browsers remains private and integral. SSL has now been replaced by TLS (Transport Layer Security), but it is still commonly referred to as SSL.

SSL vs. SSH
SSH and SSL have similarities in their goals of securing data, but differ significantly in their applications and technical implementations. Both provide encryption to ensure data confidentiality, integrity, and authenticity, and they both utilize authentication mechanisms to verify the identities of the communicating parties. They are widely used in environments that require high security.
However, their differences are notable.
-
SSL is mainly used to secure data transmitted between web servers and browsers, protecting online transactions such as online banking and shopping. SSL, when used with HTTP, operates on port 443 and relies on digital certificates issued by Certificate Authorities (CAs) for authentication.
-
SSH is primarily used for securely accessing and managing remote computers, making it a staple for system administrators who need to log into servers, manage files, and execute commands. It operates on port 22 and uses password-based or key-based authentication.
SSH's main application is in remote server management and secure file transfer, especially when combined with SFTP (Secure File Transfer Protocol). On the other hand, SSL is essential for securing websites that handle sensitive information, securing email communications, and ensuring the confidentiality of data exchanged over the internet. While both aim to protect data, their usage scenarios, operational ports, and authentication methods set them apart significantly.

Different Application Scenarios of SSL and SSH
SSL:
-
E-commerce: Online stores use SSL to secure payment transactions, protecting customers' credit card information.
-
Personal information: Websites and services that require users to enter sensitive data, such as login credentials or personal info, use SSL to ensure this data is encrypted and secure.
-
Email: SSL can also be used to secure email communication.
SSH:
-
Remote server management: System administrators use SSH to securely log into servers, manage files, and execute commands.
-
Secure file transfer: SSH can be used with protocols like SFTP (Secure File Transfer Protocol) to securely transfer files between computers.
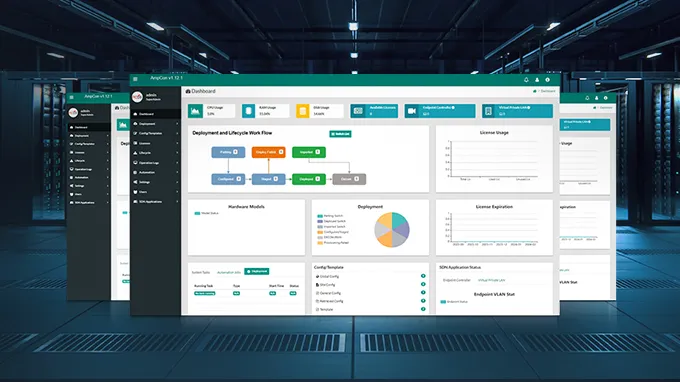
Learn more about AmpCon™ Management Platform based on SSH.
Conclusion
Understanding the differences between SSH and SSL is crucial for anyone involved in managing or securing digital systems. SSH is best suited for secure remote machine access and management, while SSL is ideal for securing data transmitted between a web server and a browser. Both are essential tools in the field of cybersecurity, each serving distinct but complementary purposes. By knowing what each protocol does and when to use it, you can better protect your digital world.
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
May 30, 2024