- English
- German
- French
- Spanish
- Japanese
- Italian
- Chinese
- Chinese (traditional)
- Home
- Blog
- Case Study
- Knowledge Center
- Glossary
- Story
- Video
- Blog Type
- Product
- Topic
- Region
Hot Search
- Product Updates
- Share FS
- PoE Switch
- Networking
- Networking Devices
- Home
- Blog
- Case Study
- Knowledge Center
- Glossary
- Story
- Video
-
- Home
- Blog
- Case Study
- Knowledge Center
- Glossary
- Story
- Video
- Blog Type
- Product
- Topic
- Region
- Home
- Blog
- Case Study
- Knowledge Center
- Glossary
- Story
- Video
- English
Hot Search
- Product Updates
- Share FS
- PoE Switch
- Networking
- Networking Devices
Network Switch and Selection Suggestions
Network Switch and Selection Suggestions
Buying the suitable network switch for your network can be a challenge. Normally, IT technicians shall know and distinguish the various network switch types and take many factors into consideration when buying network switches for current and future network. This post can be a network switch buying guide for you.
As you know, network switches connect devices like computers, printers, or servers on the same network and enable the connected devices to share information and talk to each other. There are multiple network switch types on the market by different norms. Making clear those different network switch types would be the first step for right switch buying.
Different Network Switch Types Come Into Bloom
Managed Switch vs. Unmanaged Switch
By network control and configuration, network switches can be categorized into managed switches and unmanaged switches. Managed switches have more capability than unmanaged switches. It allows you to have better control of your network and all the traffic moving through it, letting you adjust each port on the switch to any setting you desire. Moreover, managed switch offers great control over how data travels over the network and who has access to it. With SNMP (Simple Network Management Protocol) support, managed switch also allows you to monitor the status of connections and gives you statistics like traffic throughput, network errors and port status. Generally, managed switches have a remotely accessible console (command line or web interface) to allow administrators to make changes or adjustments without being in the same physical location.
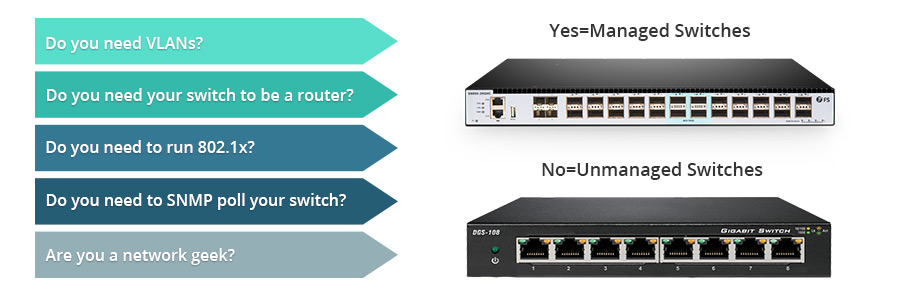 Figure 1: managed switch vs. unmanaged switch
Figure 1: managed switch vs. unmanaged switch
In contrast, unmanaged switch are plug and play. It allows Ethernet devices to communicate with one another automatically using auto-negotiation to determine parameters such as the data rate and whether to use half-duplex or full-duplex mode.
Conclusion: With managed switches, you can adjust the switch settings according to your system requirements and monitor the status of the switch, while unmanaged switch is shipped with a fixed configuration and does not allow any changes to this configuration.
Modular Chassis Switch vs. Fixed Configuration Switch
As the name implies, modular switches allow you to add expansion modules into the switches as needed, thereby delivering the best flexibility to address changing networks. On the modular chassis-based switches, you have a wider choice of interface types. For instance, you can have 10GbE line cards, which can be a combination of SFP/SFP+, X2, RJ45 and GBIC transceivers. One of the most obvious benefits of a modular chassis-based switch is redundant and highly-available hardware.
Fixed configuration switch, as its name suggests, is a standalone Ethernet switch in a self-contained enclosure. While modular switches offer the ability to swap line cards or service modules in and out as needed, a fixed configuration switch is limited to the ports and interfaces that the manufacturer shipped it with. Fixed configuration switches ship with 12, 24 or 48 Gigabit Ethernet ports and either 10 GbE or optical uplink ports. They have smaller shared port buffers which can become problematic with very bursty traffic.
Conclusion: Modular switches can add different line cards as per your requirement. However, fixed configuration switches lack this physical expandability, making it an excellent choice for the access layer of an enterprise network.
Core Switch vs. Distribution Switch vs. Access Switch
By hierarchical internetworking model, there are three layers—core, distribution and access.
Core layer is considered the backbone of the network and includes high- end switches and high-speed cables. It is responsible for fast and reliable transportation of data across a network. All other two layers rely upon it. Its purpose is to reduce the latency time in the delivery of packets. At the core layer, efficiency is the key term. So core switch has the advantage of backplane switching—the ability to pass traffic across the core without 1Gbps or even 10Gbps limits, achieving maximum performance. Generally, the backbone of the network is where switching ends and routing begins, with core switches serving both switching and routing engines. In many cases, core switches also have internal firewall capability as part of their routing feature set, helping network managers segment and control traffic as it moves from one part of the network to another.
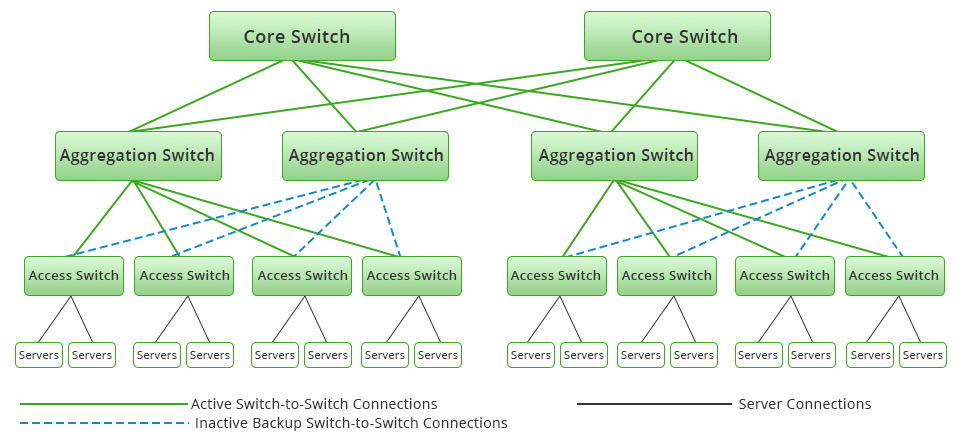 Figure 2: core switch, distribution/aggregation switch and access switch deployment example
Figure 2: core switch, distribution/aggregation switch and access switch deployment example
Distribution layer, also called workgroup layer, includes LAN-based routers and layer 3 switches. It is responsible for routing. The main goal of the distribution layer is simply cabling reduction and network management, taking the many uplinks from edge/access switches and aggregating them into higher speed links. At this layer, you begin to exert control over network transmission, including what comes in and what goes out of the network. Distribution/aggregation layer switches have stringent performance requirements, including low latency and larger MAC address table sizes. Moreover, distribution switches should offer nonstop service, such as in-service upgrades (software upgrades that don’t require reboots or significant traffic interruption) and hot-swap fan and power supply modules.
Access layer, also called desktop layer, includes hubs and standard switches. It allows workgroups and users to use the services provided by the distribution and core layers. The switches connecting directly to the end user devices are called “edge” or “access” switches. The access layer switches are not high-powered device. Edge/access switch is usually chosen based on two key requirements: high port density and low per-port costs. And they commonly support PoE, which can power many endpoint devices. Since the primary purpose of the access switch is to move around Ethernet packets, there’s no reason to buy expensive “feature-full” network switches for most buildings.
Conclusion: Core switch should always be a fast, full-featured managed switch. Distribution switch enforces all forms of network policies. They must have enough CPU speed and memory to perform all tasks at or near wire speed. Access switches typically have the highest port density , but provide the lowest throughput-per-port of all network switch types.
Layer 2 Switch vs. Layer 3 Switch vs. Layer 4 Switch
Layer 2 switch works at layer 2 of the OSI (open systems interconnection) model—the data link layer. It is a LAN device that can also be called a multiport bridge. Layer 2 switches forward Ethernet frames between Ethernet devices. They do not care about IP addresses, nor do they even examine IP addresses as the frames flow through the switch. Instead, they forward frames based on the media access control (MAC) address.
Layer 3 switch, also referred to as a multilayer switch, combines the duties of a switch and a router. It is like a high-speed router without the WAN connectivity as it has the same IP routing table for lookups, and it forms a broadcast domain. Layer 3 switch makes the use of VLANs (virtual local area networks) and interVLAN routing easier and faster due to a separate router not required between each VLAN. Layer 3 switches use a switch backplane that has bandwidth capacity far greater than that of a single or multiple Ethernet interfaces combined in a port channel. In other words, layer 3 switches improve VLAN performance as they eliminate the bottlenecks created when attempting to perform interVLAN routing using a layer 2 switch connected to a router. As the following picture shows, the layer 3 switch will still need to resolve the MAC address of PC B through an ARP request broadcasted out to VLAN 20. It then rewrites the appropriate destination MAC address and forwards the packet back out the layer 2 segment.
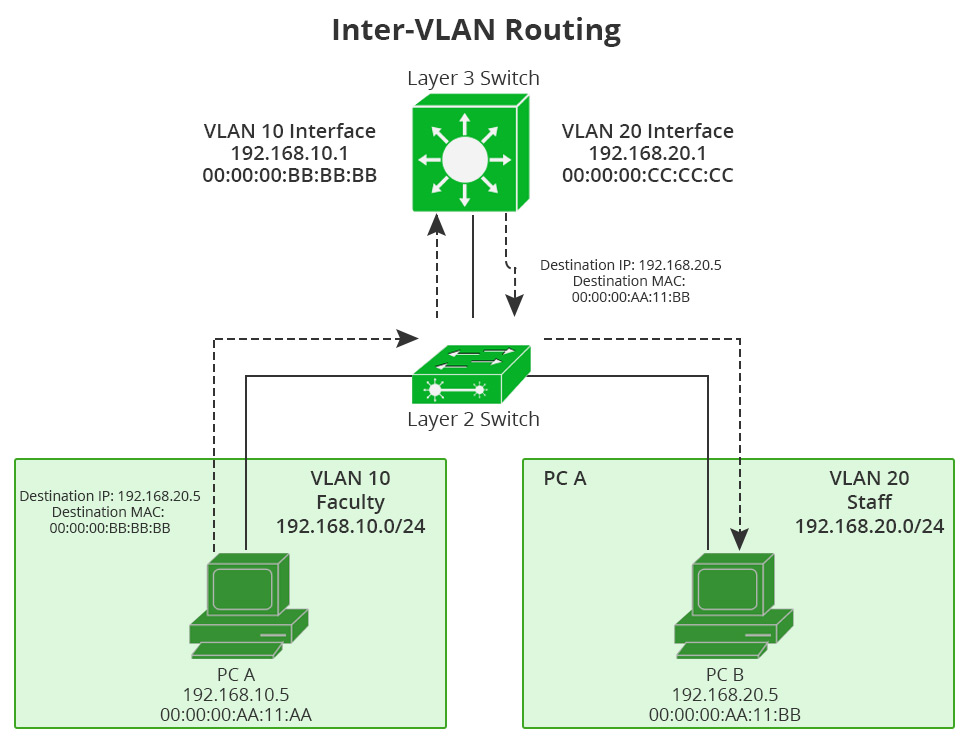 Figure 3: layer 3 switching routing between VLANs through its two VLAN interfaces.
Figure 3: layer 3 switching routing between VLANs through its two VLAN interfaces.
Layer 4 switch is primarily responsible for the analysis and control of network traffic at layer 4 or the transport layer of OSI model. Layer 4 switches make packet forwarding decisions based not only on the MAC address and IP address, but also on the application to which a packet belongs. They are capable of identifying which application protocols (HTTP, SNTP, FTP, and so forth) are included with each packet, and they use this information to hand off the packet to the appropriate higher-layer software.
Conclusion: Layer 2 switch mainly helps the traffic from devices within a LAN reach each other. Layer 3 switches are tailored for enterprise-class Ethernet networks that need to subnet into smaller networks or need traffic to cross between LANs (or VLANs). Layer 4 switch enables you to establish priorities for network traffic based on application.
How to Buy Network Switch From the Dazzling Market?
As stated above, there are many different network switch types. So what you need to know or what to consider before buying a network switch? Generally speaking, you can purchase network switches based on the following point.
Port Density and Latency
Network switches come in various shapes and sizes in terms of port types and port capacities ranging from small, 1-rack unit switches, to massive blade chassis switches filling multiple racks. Different architectures dictate how many physical ports of a particular transport type are possible. It’s up to you to figure out the number of Ethernet copper/fiber ports you need currently, as well as into the future.
Moreover, latency is also a growing consideration, because IT negotiates a shift from traffic flows that are predominantly north/south (server to user) to ones that are primarily east/west (server to server). This requires network topologies that create minimal latencies and delay to avoid application performance issues. Thus it’s critical to get an accurate estimate of current and future data flow mappings and their throughput requirements, and then choose the right size switch with sufficient backplane throughput capacity to avoid bottlenecks.
ToR or EoR Architecture
To deploy ToR (top of rack), EoR (end of row) configuration, or a full centralized witch architecture is another aspect to consider. Typically, if the cabling for an end of row configuration is already in place, it makes sense to reuse the existing wiring and deploy the larger capacity end of row switches. If new cabling will be used, you may consider top of rack options, which offer more flexibility in terms of physical port coverage across a data center.
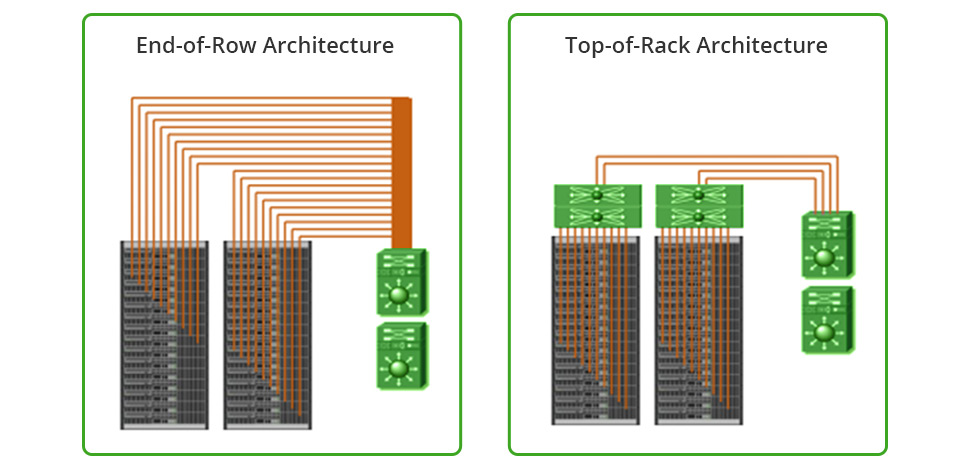 Figure 4: EoR architecture vs. ToR architecture
Figure 4: EoR architecture vs. ToR architecture
PoE or non-PoE
With the varied types of devices being connected to business networks, a network switch that can send a power signal over an Ethernet connection is more important than ever. PoE support lets a switch directly power IP phones, wireless access points, Internet Protocol security and surveillance cameras, and other devices right over Ethernet wiring. This saves businesses from running separate power cables to those devices. But when connecting to desktops or other types of devices which do not require PoE, the non-PoE switches would be cost-effective option.
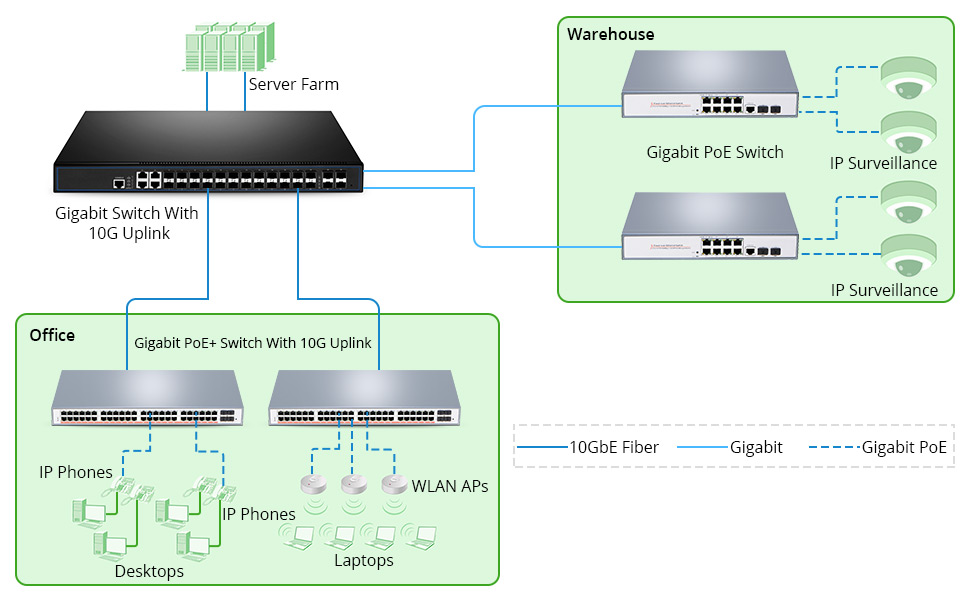 Figure 5: PoE network example
Figure 5: PoE network example
Stackable or Standalone
With network growing, you will need more switches to provide network connectivity to the growing number of devices in the network. When using standalone switches, each switch is managed, troubleshot, and configured as an individual entity. On the contrary, stackable switches provide a way to simplify and increase the availability of the network. A stackable switch is a network switch that is fully functional operating standalone but which can also be set up to operate together with one or more other network switches, with this group of switches showing the characteristics of a single switch but having the port capacity of the sum of the combined switches.
To achieve network expansion, besides network switches stack, there are another two methods—Uplink and Clustering. Simply speaking, stacking allows two or more physical switches to be combined and appear as one, and permits management of all switches and ports of the stack from a single management console. Uplink is another word for an MDI-X port—a port that allows you to run an Ethernet cable from one switch to another to add ports, distance, etc. When you cluster the switches, you can manage multiple switches through a single IP address.
Note: Please be careful about network switches in the market which are sold as “stackable” when they merely offer a single user interface, or central management interface, for getting to each individual switch unit. This approach is not stackable, but really “clustering”. You still have to configure every feature such as ACLs, QoS, Port mirroring, etc, individually on each switch. Use the following as a proof point – can I create a link aggregation group with one port in one unit of the stack and another port of that group in another unit of the stack? Can I select a port on one unit in the stack and mirror the traffic to a port on another unit of the stack? When I configure an ACL for Security purposes, can I apply that to any port on any unit in the stack? If the answer is “No” to any of these questions, you’re probably not working with a stackable switch.
Think Twice Before Buying Network Switches
To buy network switches that will ensure the best network performance but also continue to perform into the future is no easy task. You need to consider a great deal when purchasing network switches. The best way to approach buying network switches is to understand the network switch types of features vendors offer first and determine which are required by the network in place. Then you can evaluate vendors based on the quality of support they provide and their paths toward future-proofing your investment.
Related Articles:
Multi-Gigabit Switch for Growing Enterprise Campus Network
FS S5860-24XB-U PoE Switch Guarantees High-reliability Power Supply
You might be interested in
Email Address

-
PoE vs PoE+ vs PoE++ Switch: How to Choose?
Mar 16, 2023














